Simplify endpoint security: Endpoint Detection and Response — designed for service providers
Organizations of all sizes need advanced security controls to combat today’s cyber threats. But unfortunately, most EDR/XDR solutions capable of countering these threats and risks are too complex and costly to operate. Moreover, they require multiple point solutions for complete protection and businesses continuity. With Acronis there’s a better way.
Designed for service providers, Acronis EDR enables you to simplify endpoint security — rapidly detect and remediate advanced attacks while ensuring unmatched business continuity. Eliminate the cost and complexity of multiple point products and enable your team with one complete cyber protection solution that is simple to manage and deploy.
-
Integrated backup and recovery capabilities for unmatched business continuity
- Integrated backup and recovery capabilities, providing unmatched business continuity where point-security solutions fail
- Streamlined single-click remediation and recovery
- Complete, integrated protection across the NIST security framework — Identify, Protect, Detect, Respond, and Recover — all from a single solution.
-
Complete cyber protection solution – designed for MSPs – in a single agent
- Quickly and easily launch new services using a single Acronis agent and console — to deploy, manage and scale
- Easily scale across multiple clients while preserving healthy margins and minimizing OpEx — no need for a large team of highly skilled people to operate
- Partner with a vendor focused on your success and enablement — not competing with you for business.
-
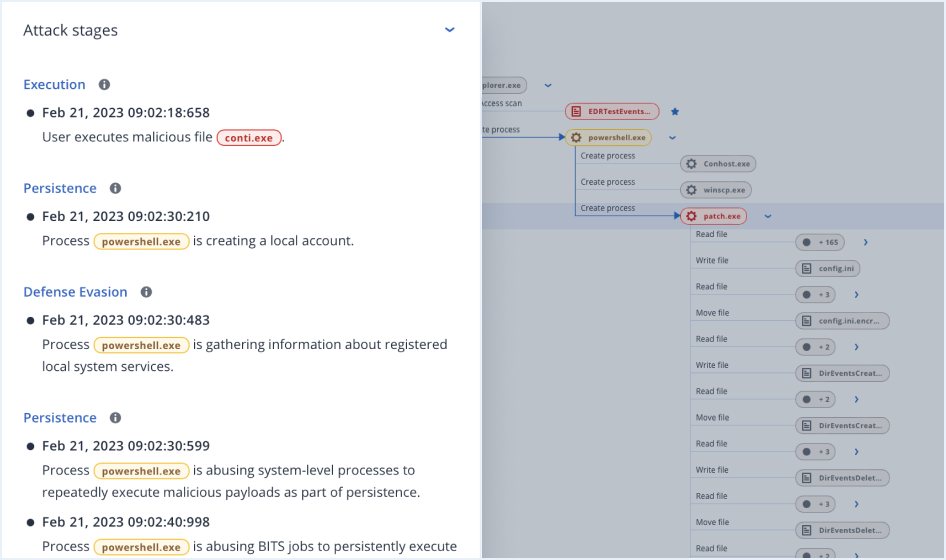
Optimized attack prioritization and analysis for rapid response
- Streamline investigations with prioritization of potential incidents and reduced alert fatigue
- Unlock minutes-not-hours analysis at scale, with automated correlation and AI-based guided attack interpretations
- Increase visibility across MITRE ATT&CK® to rapidly grasp attack analysis and impact, including how an attack got in, what harm it caused, and how it potentially spread.
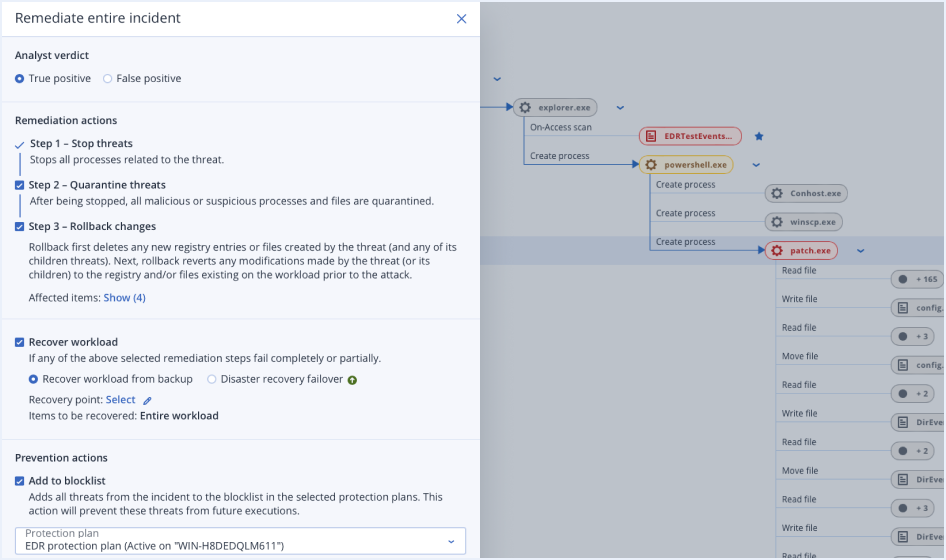
Unmatched business continuity with a single-click response
-
Remediateby network isolating endpoints, killing malicious processes, quartering threats, and rolling back attack changes.
-
Investigate further
using remote connections and forensic backups
-
Prevent future attacksby blocking analyzed threats from execution and closing open vulnerabilities
-
Ensure business continuity with integrated recoveryincluding attack-specific rollback, file- or image-level recovery, and disaster recovery
Rapid investigations and threat response
-
Cut investigation and response times from months to hours* and remove the need for large security teams to operate
-
Increase visibility with AI-based attack interpretations across MITRE ATT&CK® – rapidly grasp how an attack got in, hid its tracks, what harm did it cause, and how it spread
-
Get a prioritized view to investigate suspicious activities – rather than flat list of all alerts
-
Focus threat hunting using an emerging threat intelligence feed to search for IoCs
Complete protection across NIST framework with a unified platform
Unlike pure-play cybersecurity solutions, Acronis Cyber Protect Cloud brings the full power of its platform with integrated capabilities across the NIST framework for unmatched business continuity.
-
Identify
You need to know what you have to fully protect it, and investigate into it. Our platform includes both inventory and data classification tools to better understand attack surfaces. -
Protect
Close security vulnerabilities using our threat intelligence feed, forensic insights, and natively integrated tools across the broader Acronis platform like data protection maps, patch management, blocking analyzed attacks, and policy management. -
Detect
Continuous monitoring for security related events using automated behavioral- and signature-based engines, URL filtering, an emerging threat intelligence feed, event correlation and MITRE ATT&CK®. -
RespondInvestigate suspicious activities and conduct follow-up audits using a secure, remote connection into workloads or reviewing automatically saved forensic data in backups. Then, remediate via isolation, killing processes, quarantining, and attack-specific rollbacks.
-
RecoverEnsure systems, endpoint data and the client business are up and running using our fully integrated, market-leading backup and disaster recovery products and solutions.
Unlock the latest in EDR: Acronis Academy Tech Associate course
Discover advanced endpoint security, emphasizing proactive malware prevention and cutting-edge detection techniques. Explore cloud-managed EPP (endpoint protection platform) features, EDR and EPP convergence, and gain valuable insights into essential cybersecurity concepts.




